
How to Bulletproof Your Business from Dangerous and Modern Cyber Attacks
Have you heard of the expression, “He’ll never know what hit him?”
That’s what people say when they see someone ill-prepared to face an incoming disaster.
Of course, that is not how you want your business to be in the face of cyber attacks.
In 2018, Verizon’s Data Breach Investigation uncovered that 58% of cyber attack victims were small businesses.
Modern-day hackers target small businesses more than big ones because most of these small businesses have minimal or basic security, making it easier to steal their sensitive information.
The scariest part is your business might be in the middle of a cyber attack right now without you noticing. You need to ensure protection from threats like brand infringement, for example, where your brand details get stolen and another company uses them as their own.
A cyber attack can have a colossal impact on your business and may even lead to its demise.
If you want to safeguard it, you need to arm yourself with the following tips on how to bulletproof your business from dangerous and modern cyber attacks.
1. Ensure That Your Wi-Fi Is Secure
Your Wi-Fi network is the easiest channel to infiltrate and then gain access to all your business information. Scary, right? So the safest way to keep your network secure is by protecting it with a strong password.
Make your Wi-Fi password strong by including as many different character combinations as possible and if you can, limit the number of employees with direct access to your password.
Also, avoid having your customers and employees use a single network. Offer a guest network for your customers to prevent other users from gaining access to your business network, information, printers, computers, LAN, etc.
However, if you are traveling and doing business online, you will have no control over public networks in hotels and other establishments.
It’s vital to ensure data protection when you are conducting your business from somewhere other than your office by using your phone’s mobile data or a VPN.
2. Segment Your Network
Your network will have a lot of connected users, but you can limit their access depending on their functions.
Ensure that your employees have access only to information they need to perform their jobs by applying role-based access control (RBAC). For instance, your marketing manager should not have access to financial accounts only intended for C-level executives.
With the RBAC model, roles are based on some factors like job competency, responsibility, and authorization among other things, giving you the option to designate different users as an administrator, end user, or a specialist user.
Moreover, by using RBAC, you can limit access to your computer resources based on specific tasks like the ability to edit, create, or view files.
Segregate your network into different smaller networks for specific company departments and with varying access levels. Segregation will also help you contain any network malfunctions and attacks since not all of your networks will be affected.
By segmenting your computer network, you can manage traffic to reduce congestion and improve network performance and choose which information to isolate, thereby improving your online security.
3. Implement Two-Step Authentication
Two-step authentication procedures offer added layers of protection to an online system because users are required to verify their identity twice.
The first step asks users for their sign-in details, like the username and password, and the second step requires user identity confirmation through specific personal information.
Common security questions like the name of your first pet, however, can still be easily deciphered by hackers, so the two-step authentication procedure makes use of other forms of confirmation like fingerprints, QR codes, email codes, SMS codes, and one-time passwords.
Two-step authentication is highly effective in protecting your online information from hackers, and platforms like Twitter, Facebook, and Google even use them to ensure the security of their users’ accounts.
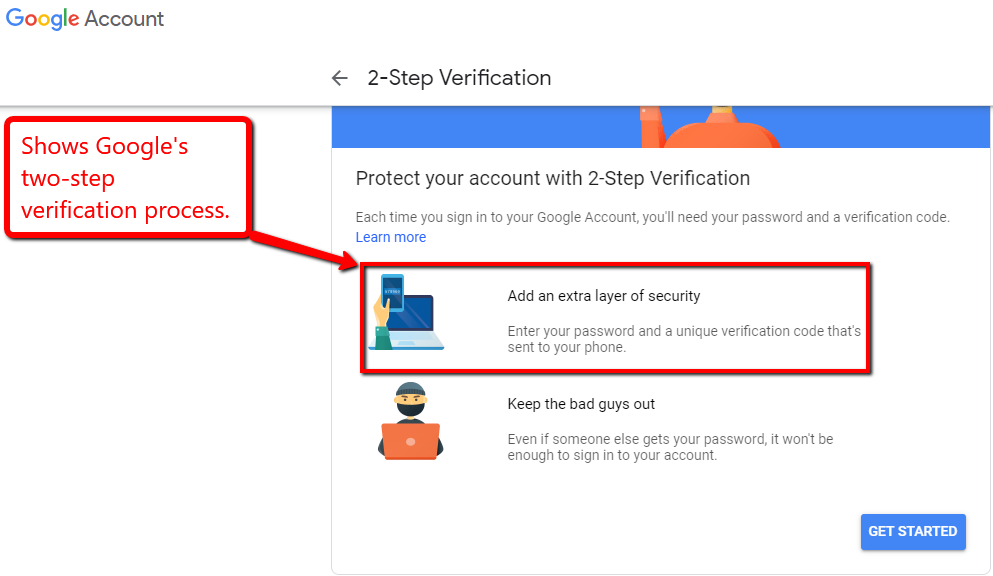
Ensure that any device (mobile phones and laptops) that you assign to your employees requires two-step authentication to protect critical business and customer information from outsiders and deny them access in case the device is stolen or lost.
4. Utilize SSL Encryption
To keep your website safe from hackers and strengthen your online protection, you need to set up safeguards to ensure maximum security. One way is through an SSL certificate.
An SSL certificate encrypts connections between a browser and your server. You know it’s active if your site URL shows HTTPS instead of HTTP and has a padlock icon beside it.
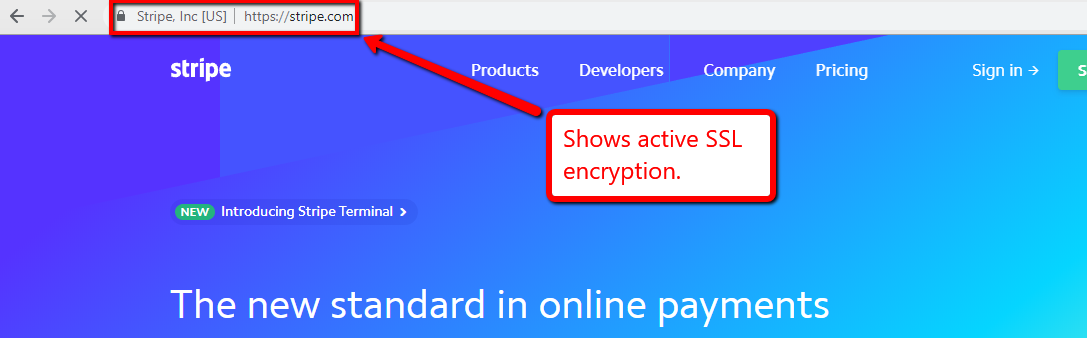
Sensitive information such as credit card details and passwords can be transferred securely during online transactions if you have SSL encryption in place, making it a vital factor in preventing hackers from accessing confidential information.
5. Apply SIEM Technology
It’s essential to be vigilant of cyber-attacks and to check your network for possible threats regularly.
A great approach to help you monitor your online safety and security is by using Security Information and Event Management (SIEM).
SIEM tools allow you to see the security landscape of your network by gathering all security log data from various applications and software elements, security controls, and host operating systems.
SIEM also analyzes extensive security log data to identify any security threats and attacks.
Cybersecurity services like Bulletproof, allow you to virtually own an outsourced Security Operations Center (SOC), which can run penetration testing and managed SIEM on a 24/7 basis.
As you work with these third-party providers, you can enjoy the benefit of having highly-skilled professionals monitor the health of your network 24/7.
6. Train Your Employees on Security
According to the Annual Cyber Security Report 2019 from Bulletproof, an average of 14.5 billion spam messages are sent in a day, and 73% of these are phishing emails. Phishing emails normally target unsuspecting employees to gain access to your sensitive information.
Your online reputation lies on how equipped your employees are at dealing with threats and cyber attacks since they have access to your sensitive business information. It’s crucial for them to catch security incidents and report them.
If your employees are trained on which dangers to look out for, they can help you prevent attacks before they happen or at least mitigate the possible damages to your business.
Here are two things your employees should be trained in to strengthen your online security:
a. Phishing. This is a security issue that your employees should be highly aware of. Hackers disguise themselves as reputable organizations or entities through ads and emails to gain control over sensitive information like credit card details and passwords.
Most phishing emails attempt to convince users that they are from legitimate sources and that the matter they are presenting needs your urgent attention.
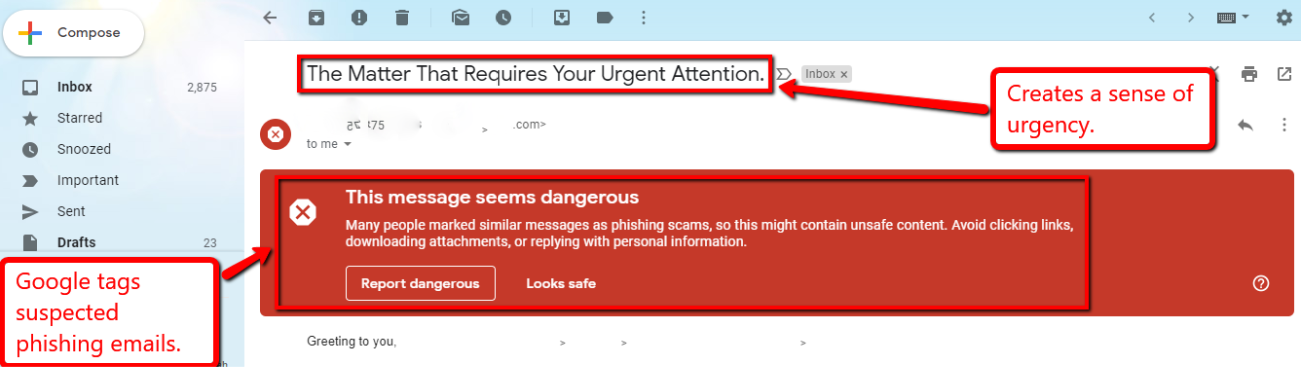
In the screenshot above, Gmail alerts users of emails that have been reported as a phishing scam. These fraudulent messages request users to click on links or download an attachment that may look harmless to the untrained eye.
Your employees should learn to recognize phishing emails right away. Make it a part of your company policy to be cautious of unsolicited emails to avoid security breaches.
b. Strong Password. Require your employees to use a strong business account password by including as many unique characters and numbers as possible.
Encourage them to use separate passwords for the business and their personal accounts. If they use the same passwords for both accounts, you run the risk of compromising your company data in case their password gets leaked.
Also, prohibit them from sharing their company passwords with anyone to limit access to sensitive business information and protect trade secrets.
Final Thoughts
Online safety and security should be a priority for your business to keep you and your customers’ assets and sensitive information protected.
You can safeguard your business from hackers and cyber attacks by following the tips discussed in this article.